Contact Centers (4)
BLOG LISTINGS
November 27, 2024
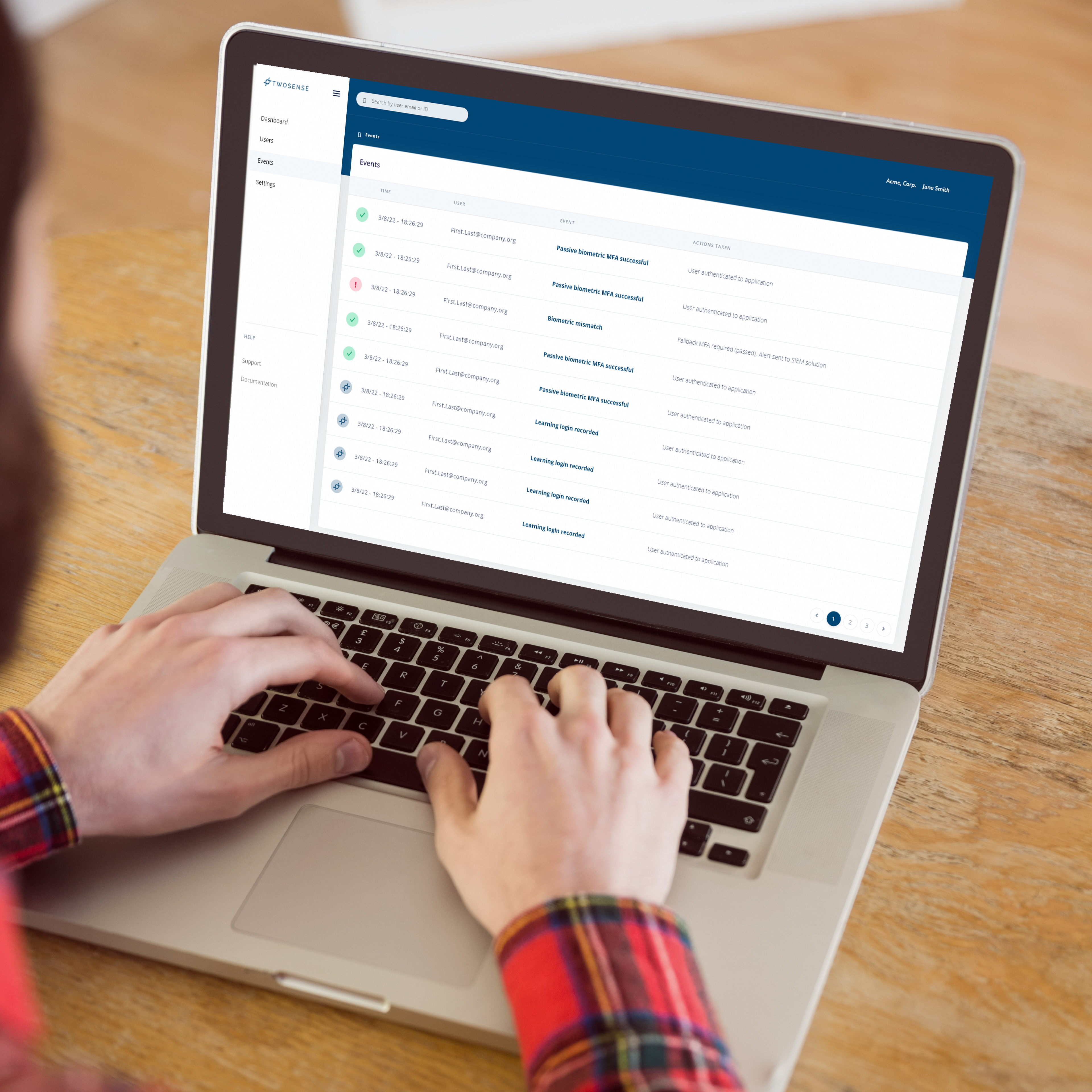
You’ve probably heard IT and security teams buzzing about continuous authentication, also called continuous access...
November 7, 2024
As cyber-attacks become more sophisticated and the cost of a breach increases, contact centers are forced to explore...
October 9, 2024
Contact centers play a huge role in customer satisfaction and are essential to operations for large consumer-facing...
September 18, 2024
Introduction The position of Chief Information Security Officer (CISO) is critical, especially within Business Process...
July 22, 2024
Information security is critical, especially in Business Process Outsourcing (BPO) contact centers, where massive...
Posts by Tag
- 2FA (8)
- Agent Identity (4)
- Agile (1)
- Authenticator Abuse (1)
- Automated MFA (6)
- Banks (1)
- Behavioral Authentication (4)
- Behavioral MFA (27)
- Biometrics (20)
- BPO (22)
- Burnout (1)
- CCaaS (1)
- Clean Desk MFA (1)
- Compensating Controls (2)
- Compliance (18)
- Contact Centers (59)
- Continuous Access Evaluation (12)
- Continuous Authentication (89)
- Continuous Identity Verification (1)
- Continuous MFA (27)
- Cryptocurrency (1)
- Culture (3)
- Cyber Insurance (1)
- Cybersecurity (27)
- Data Breach (12)
- Data Science (1)
- Deep Work (1)
- Epic (1)
- Flow State (1)
- Fraud Prevention (1)
- Hard Token Alternative (1)
- Hard Tokens (1)
- Health Systems (1)
- Healthcare (4)
- HIPAA (2)
- Hospitals (9)
- IAM (1)
- Identity Access Management (4)
- Infosec (14)
- Machine Learning (5)
- Mental Health (3)
- MFA (5)
- MFA Fatigue (1)
- Multi-Factor Authentication (49)
- Pass-Through Authentication (1)
- Passive Biometrics (10)
- Passive MFA (1)
- Password Sharing (2)
- Passwordless (10)
- PCI Compliance (18)
- PCI DSS (14)
- Phishing (5)
- Phishing-Resistant MFA (12)
- Preparedness (1)
- Prompt Bombing (3)
- RFPs (1)
- Session Security (1)
- Shared Workstations (3)
- SOC2 (1)
- Social Engineering (4)
- Software MFA (1)
- Twosense Team (2)
- Unauthorized Users (1)
- Unphishable MFA (11)
- WAHA (1)
- Webinar (1)
- WFH (4)
- Zero Trust (10)
Recent Posts
Sign Up for our Blog
We will never share your email address with third parties.