Choosing the right fit for a contact center's MFA is easier said than done. When it comes to deciding which security solution is worth investing in, there are a multitude of factors that need to be considered: cost, scalability, ease of deployment, and whether or not it meets compliance standards.
Given that cardholder data is being handled on a daily basis, most BPOs choose to limit mobile phones on the floor – as suggested by PCI SSC – as a security precaution. This makes implementation a challenge when it comes to using modern MFA solutions, as most rely on the user having a mobile device. This presents another often overlooked problem: If a mobile phone is required for security procedures, and an employee does not have a smartphone, the organization would be required to provide one which is costly and unsustainable long term.
While some organizations are willing to take the risk and allow mobile devices on the contact center floor for MFA, it is not PCI DSS compliant. Noncompliance risks a variety of consequences: $500,000 fines, needing to hire PCI DSS auditors which can cost $100,000 a pop, or worst of all, damages to the brand's reputation which can result in a loss of clients.
For years, hard tokens have been the alternative to mobile-centric MFA, but tokens present their own unique challenges. In addition to being a costly investment for the token itself, organizations need to remember that like any other device they can get lost, broken, or have the battery die. Hard tokens also require a significant time investment. In an industry with an average 150% annual churn, the time and effort required to order, issue, and reissue tokens can be unsustainable.
Whether hard token or mobile-based, traditional MFA methods all have one thing in common: interruptions. Both require the agent to stop what they are doing each time they complete an MFA challenge. If organizations are following best practices such as 15-minute lockouts, this means agents are interrupted repeatedly throughout the day. This time can be better spent actually helping customers.
Twosense Passive and Continuous MFA is changing the way that BPOs go about identity security. Designed specifically for call centers, Twosense MFA is a no-phone, software-only multi-factor authentication powered by behavior biometrics.
Organizations can deploy MFA in a contact center environment for a team of 100 for as little as $3600 for the year. Unlike hard tokens, Twosense does not require organizations to assign, reassign, or manage seats or devices. By design, Twosense only counts people actively using the software in the last 30 days reducing significant friction for administrators and reducing wasteful spending.
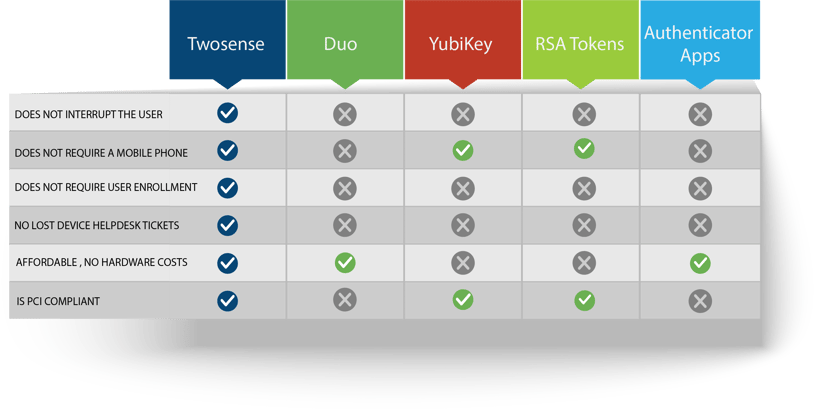
Implementing behavioral biometrics such as Twosense Passive MFA or Continuous MFA into contact centers’ identity security postures enables BPOs to do what was previously impossible: deploy MFA everywhere, to every user without increasing user friction or increasing security costs. An added bonus is that since each biometric factor is unique to each user, both Twosense Passive and Continuous MFA are phishing-resistant by design.
To learn more about how Twosense can reduce your security costs, bring your contact center up to compliance, and provide better security, please request your private demo here.


.jpeg)