In contact centers, security is more important than ever before. Still, strict clean desk policies and the cost of hard tokens like YubiKeys have made multi-factor authentication (MFA) difficult to impossible to implement. For most contact centers, there has been a way to thread this needle and still conform with compliance. However, in less than one year, PCI 4.0, a revised compliance requirements document, will become effective, creating a major disruption to the IT and Security teams operating contact centers. Primarily, it enforces MFA for just about every access request, which creates its own problems, and although Requirement 8 won't be enforced until March 2025, implementing the necessary solutions should not wait. One of the other areas where security and compliance are about to become dramatically more difficult to satisfy is password management, which we’re going to talk about here.
With BPOs largely servicing customers who are outsourcing their customer service, they will predominately be subject to the requirements as they pertain to third parties, which means agents will see an increase in password rotations for systems and applications owned by their clients. This includes things like CRMs and other client-owned applications.
This poses some challenges for both the BPO and its customers. One result of this requirement is that when agents forget their password after a rotation, they will call the customer's helpdesk to initiate a password reset.
The new password policy requirements are as follows:
8.3.6 If passwords/passphrases are used as authentication factors, they meet the following
minimum level of complexity:
-
- A minimum length of 12 characters (or IF the system does not support 12 characters, a minimum length of eight characters).
-
- Contain both numeric and alphabetic characters.
8.6.3 Passwords/passphrases for any application and system accounts are protected against
misuse as follows:
“ Best practices are to consider password changes at least once a year, a password/passphrase length of at least 15 characters, and complexity for the passwords/passphrase of alphanumeric characters, with upper- and lower-case letters, and special characters.”
This means organizations will rotate once a year rather than once a quarter.
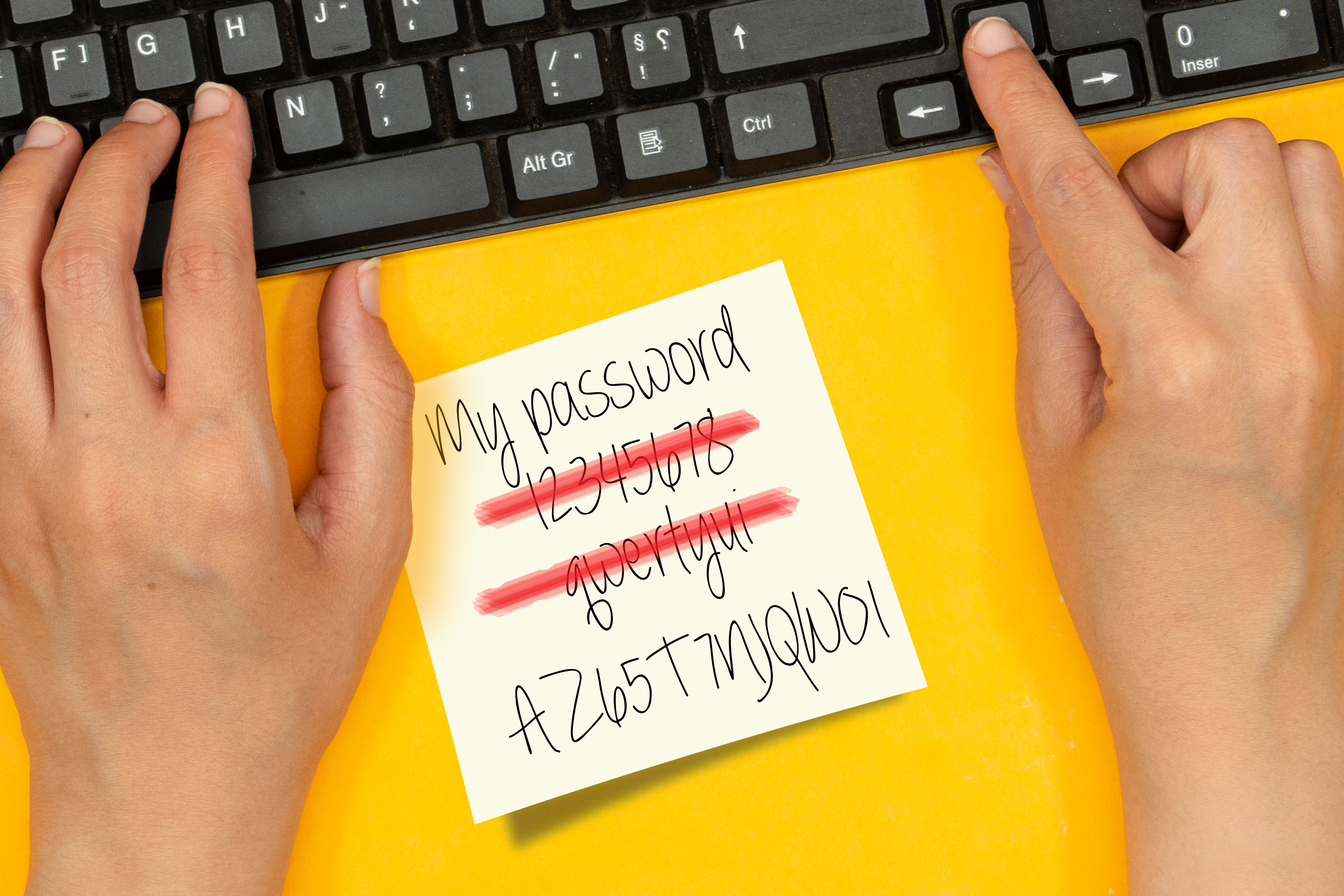
If you’re not already implementing complex passwords, this will be a major lift to get all your systems to implement the change and have all your users reset their credentials to meet the new standards. The bad news is that this process will almost certainly result in a heavy IT workload over the following few weeks, spiking credential resets as users struggle to adapt.
The good news, however, is that once the initial flood of helpdesk tickets dies down, the relaxed rotation period of one year will probably result in a 75% reduction in credential resets at the helpdesk over time. If you stagger the rotation period across your users, you can avoid another huge peak in ticket loads next year when everyone’s credentials reset at the same time, and the new complex passwords drive up locked accounts again. We recommend getting started on this early and rolling it out to users' tranches over a year.
There is an extra sub-requirement for credentials for outsourced call centers and business process outsourcing (BPOs) specifically.
8.3.10.1 Additional requirement for service providers only: If passwords/passphrases are used as the only authentication factor for customer user access (i.e., in any single-factor authentication implementation) then either:
Passwords/passphrases are changed at least once every 90 days, [...]
[...] OR The security posture of accounts is dynamically analyzed, and real-time access to resources is automatically determined accordingly.
While this may be a pain… it gets logistically worse. In the infrastructure of BPOs, often, for reasons outside its control, agents need to have single-factor (password only) access to the customer’s infrastructure. This is protected with VPN tunnels, Citrix, and a host of other technologies, but sometimes it just has to be this way. However, PCI DSS v4.0 places the burden of responsibility for awareness, notification, enforcement of, and therefore liability for, credential rotation on the BPO.
8.3.10 Additional requirement for service providers only: If passwords/passphrases are used as the only authentication factor for customer
user access to cardholder data (i.e., in any single-factor authentication implementation), then guidance is provided to customer users including:
-
- Guidance for customers to change their user passwords/passphrases periodically.
-
- Guidance as to when, and under what circumstances, passwords/passphrases are to be changed.
Simply put, as a BPO, the organization is responsible for ensuring that its customers rotate its agent's credentials in accordance with PCI DSS v4.0.
This means things will be tricky in those environments where BPO agents are authenticated into customer infrastructure with a username and password only. The password requirements remain the same, complex, but rotated. This change will also almost certainly be painful for both BPOs and BPO customers as credential resets mount, and the customer will feel the impact. There is, however, a way around this:
Sign Up For Full Access To The Blueprint To PCI DSS v4.0 Multi-Factor Authentication.
If you can show auditors that you’re dynamically assessing identity risk in real-time, you’ll be allowed to relax rotation to once a year. According to NIST 800-207 Zero Trust Architecture, a dynamically analyzed security posture is a continuous and real-time evaluation of an organization's security risk posture. This means an organization's security posture is assessed automatically and in real-time based on various factors such as user behavior, system configurations, network traffic, and threat intelligence.
Twosense Continuous Multi-Factor Authentication does exactly this. Twosense’s cloud-based machine learning platform analyzes the passive biometric data to learn who your users are, creating a unique profile for each user. Whenever a user passes an MFA challenge, each model continues to learn and adapt to changing behaviors. The more behavior is observed, the more confident Twosense can be that the user is who they claim to be. When the model is mature, Twosense can validate the user's identity and create a baseline of trust.
With Continuous MFA, the user’s recent behavior is continually and automatically analyzed compared to their behavioral biometric model. This means that multifactor checks are being performed on the user continuously throughout the day instead of waiting for the moment the user is authenticating to an application. This is how Twosense is able to meet the requirement of “ having the security posture of accounts dynamically analyzed and real-time access to resources be automatically determined accordingly.” With this requirement met, you can relax credential rotation schedules to annual. Most BPOs have high employee turnover, so you might rarely need to rotate a password, and only for your best employees if you can thread this needle right.
Ultimately, for BPOs looking to mitigate the responsibility of having to request every 90 days that their customer rotate their agent's passwords, Continuous MFA is a must-have solution in its technology stack.
** This blog has been updated to provide clarity regarding PCI DSS v4.0 implementation timeline