With PCI v4.0 making it clear that multi-factor authentication is mandatory for everyone and all network access, it is important to consider how other updates in PCI Requirement 8 will impact security friction. One of the many new additions to PCI 4.0 is an alignment with NIST 800-63B guidance on 15-minute timeouts. In PCI 3.2.1, 15-minute timeouts were a recommendation but not a requirement. In PCI 4.0 Requirement 8.2.8 states:
If a user session has been idle for more than 15 minutes, the user is required to re-authenticate to re-activate the terminal or session.
The addition of the requirement for 15-minute timeouts is aimed at reducing the risk of unauthorized access to sensitive cardholder data. If an agent's session has been inactive for more than 15 minutes, the agent must re-authenticate to reactivate the terminal or session. This is to help prevent unauthorized individuals from accessing cardholder data if an agent leaves their workstation unattended for an extended period, or their active session is somehow illegitimately accessed (e.g. session or token hijacking).
Implementing mandatory timeouts after 15 minutes of a user session being idle, compounded with other new requirements, will drastically increase the security friction agents experience daily. The most obvious disruption the implementation of 15-minute timeouts will have is on an agent's workflow. It will significantly impact productivity if agents have to re-authenticate every 15 minutes, leading to frustration and a negative customer experience.
Sign Up For Full Access To The Blueprint To PCI DSS v4.0 Multi-Factor Authentication.
Depending on the authentication method being used, logging back into the system after a timeout will take additional time and effort for the agent. This can be particularly problematic when the contact center is experiencing high call volumes or long wait times for customers, as it can lead to increased handle times and decreased efficiency.
One complication is that the new PCI requirements have changed their view on what constitutes a session. It has been made clear that a VPN or network connection is one session, and the Card Data Environment (CDE) is another, each requiring its own multi-factor challenge for access, and each now expiring strictly after 15 minutes of inactivity. Furthermore, for agents connecting to multiple CDEs, each of those is regarded as its own session as well. Leaving one CDE unused for 15 mins (for example, if the tab or application is minimized) will require full MFA to reinitiate that session while stepping away from the machine for, say, a bathroom break will require an MFA challenge to reconnect to the network, and another for every CDE reconnection.
Ultimately, the addition of 15-minute timeouts in PCI v4.0 will wreak havoc in contact centers attempting to maintain compliance with traditional multi-factor authentication solutions – for both agents and their supervisors. The solution to mitigating the impacts of these requirements is to deploy a multi-factor authentication solution that automates the MFA challenge response while continuously authenticating agents' identities throughout the day.
It is crucial to note that automating MFA to combat 15-minute timeouts is impossible without continuous authentication.
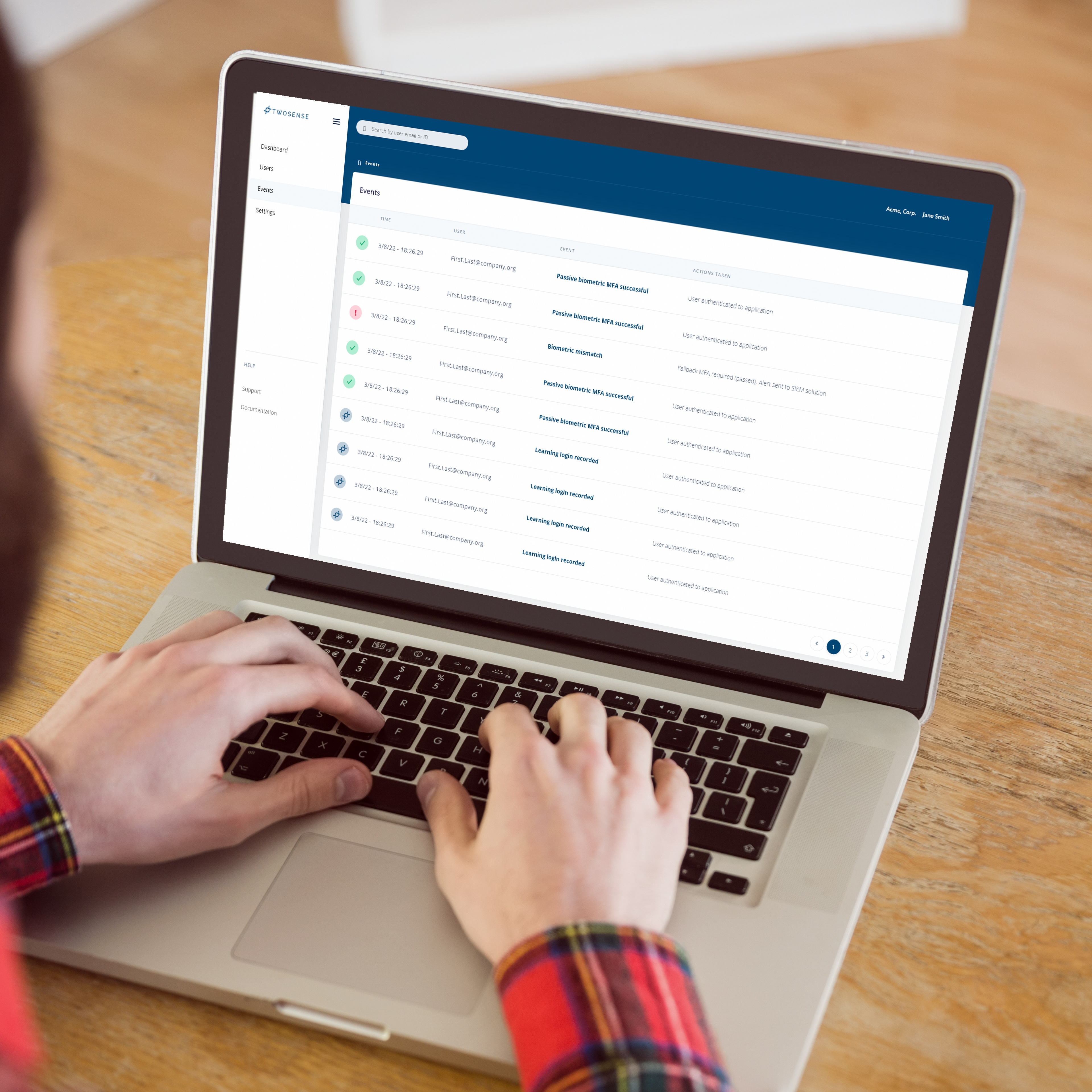
Twosense Continuous MFA is uniquely designed software for contact centers that does not require a mobile device, hard token, or additional training. Twosense creates a unique biometric profile for each user. Each model learns and adapts to changing behaviors to biometrically authenticate the user at every MFA challenge in an invisible way. The more behavior is observed, the more confident Twosense can be that the user is who they claim to be. Continuous MFA validates the user's identity and authenticates them not by what they’re doing but by how they’re doing it, generating a level of trust for every interaction in the background. That trust score is then used to authenticate the user continuously throughout the day or flag unauthorized access. Twosense solution can be deployed as an agent on each user’s machine– deployment is as simple as three easy steps that can be done in a single afternoon.
Continuous MFA ensures the correct agent is behind every keyboard, allowing agents to work frictionlessly throughout the day. Should an agent walk away from their station, share their credentials, or otherwise have their device or station compromised, Continuous MFA gives contact centers the security of knowing a behavioral mismatch will occur, ending the unauthorized user's session immediately. We give BPOs better security overall that can be demonstrated to their customers.