A recent study by Nominet shows that the average tenure for Chief Information Security Officers is only 26 months due to high stress and burnout. The same report found that this is causing physical, mental health, and even dependency issues. InfoSec professionals across the board are subject to higher levels of stress and the problem continues to grow. A resolution will require support from within the organization, and the tools to change the antagonistic mindset between InfoSec and the workforce.
Numbers reported by Nominet show that CISOs are burning out at alarming levels. From a sample of 800 CISO’s from companies in the US and UK, it has been found that:
- On average 88% reported “moderate to tremendous” levels of stress.
- 48% reported an impact on their mental health.
- 23% say it forced them to seek medication or experience substance abuse.
The end results reveal that the average tenure for CISO’s currently sits at 26 months, which is shockingly low, especially when compared to the average tenure of other C-level suite positions which is currently 5.3 years.
While many companies are beginning to adopt CISO roles due to increasing cybersecurity threats, integration hasn’t exactly been a seamless experience leading to significant friction. These roles often come with low budgets, long hours, and a lack of power on executive boards, while having to deal with the constant threat of cyber-attacks leading to the observed stress and burnout. Chief Information Security Officers are tasked with continuously protecting the organization where nobody notices when things go right, however, when something goes wrong bear much of the blame.
Another interesting part of the study shows that 29% of CISOs would be fired in the event of a data breach, despite the inevitability of one, and 20% would be fired even if they were responsible or not. Stuck between a rock and a hard place, a CISO is truly a tough and often thankless position to be in.
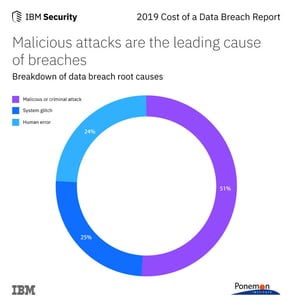
Looking at the details, it’s not surprising that most CISOs tend to burn out quickly. What makes this even more interesting is that almost a quarter of data breaches are actually due to human error. What this means is that no matter how well you set up your security protocols, a data breach can still happen due to human factors.
In fact, phishing and stolen user credentials are the attack vector for the majority of hacking attempts. The front-line tool to prevent these attacks is Multi-Factor Authentication (MFA). However, the problem is that MFA creates user friction in the form of authentication challenges, putting the rest of the company at odds with the CISO and InfoSec professionals, even up to the C-suite and board level. About 74% of organizations receive complaints about MFA which causes boards and executives to be hesitant in strict implementation. The result is only a partial deployment of MFA, leaving the organization vulnerable to attack and the CISO fearing for their job, but unable to push for better security.
At Twosense our mission is to solve the fundamental problem associated with MFA. Twosense has created a solution that removes the human variable from identity security and acts as a layer that can be deployed into any infrastructure. This software works on the user’s behalf to run continuous authentication via passive biometrics. Companies don’t have to ditch pre-existing systems because Twosense works with what is already in place to increase the overall effectiveness, without negatively impacting the user’s experience and elevating stress from CISO’s.
Our software integrates with existing login workflows to reduce authentication challenges by 95% while running MFA all the time. This empowers organizations to do what was previously impossible: increase MFA security while also automating the challenge-response to preserve user experience and productivity.
Reach out to see how Twosense can help you get better security with a better user experience.


.jpeg)