Contact center security teams are fighting an uphill battle. When it comes to multi-factor authentication, they’re expected to deploy effective, compliant, and friction-free MFA to agents in highly restrictive environments. There is no shortage of difficulties when it comes to contact center agent identity.
A common complication for BPO security teams is that sometimes the BPO is not the decision maker when it comes to which solutions are implemented. Many organizations that outsource their customer service determine which software or solution will be deployed to agents.
In a situation where the BPO has the decision-making power, they face the hurdle that the current MFA solutions don’t work in a contact center environment. Standard MFA requires a mobile device, and since mobile devices are banned from being on the floor by mandated “clean desk policies,” those solutions won't work. This leaves many contact centers looking at email MFA, which does not meet compliance standards.
Hard tokens are often seen as the last resort in order to implement PCI-compliant authentication for agents. Still, tokens require two significant investments 1) the purchase of the devices– 100 Yubikeys cost about $4500 and 2) someone to issue, maintain, collect, or replace them in the inevitable event an individual is let go, quits, or their token is lost or broken.
Contact centers also have a lot to contend with internally when it comes to identity security. Contact centers have some of the highest churn rates of any industry. This makes solutions that require enrolling, ongoing education, and maintenance, like assigning and unassigning seats or tokens, almost impossible to manage and scale.
These challenges often result in no MFA being used at all, which is disastrous.
Unfortunately, it is often only when a security incident has occurred that MFA vulnerabilities come to light. After all, MFA is one of the first lines of defense when protecting contact centers from breaches. BPO contact centers are often targets of threat actors due to the volume of PII (personally identifiable information) they handle. The consequences of having a poorly configured MFA, or no MFA at all –particularly in the event of a breach– are significant.
Ultimately, at this stage in the game, every contact center should know that multi-factor authentication is not negotiable. MFA is required for all organizations that store, process, and/or transmit cardholder data by PCI DSS—making maintaining PCI compliance paramount.
Being found in non-compliance can result in monthly penalties, which can range from $5,000 to $500,000, to required audits which can start at $250,000, to legal action and loss of revenue. However, the worst thing that can happen is reputational damage resulting in losing the trust of valued customers.
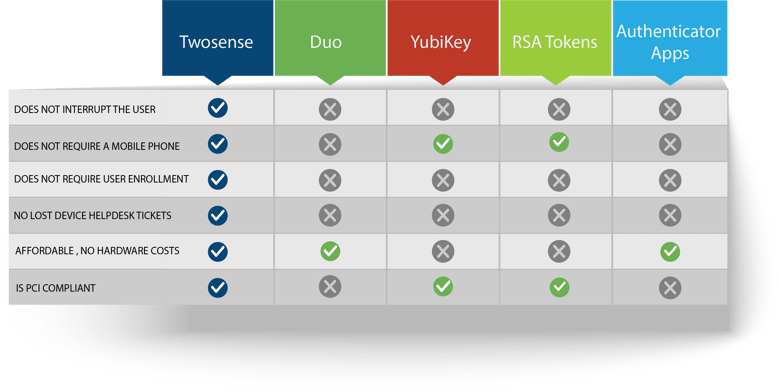
So, the question remains: what solutions are available in a highly restrictive industry where the majority of available solutions don't work? Continuous Authentication.
Twosense has developed a software-only MFA designed for the contact center environment. Our solution automates MFA challenges using passive biometrics to authenticate agents. Automating MFA has been shown to recapture 40 minutes per agent per month, allowing agents to spend more time helping customers.
Deployed as a browser extension (Chrome and Edge) or a Windows agent, this is ideal for contact centers because it doesn’t require a phone or a hardware token as the software is installed on the user’s browser, workstation, or virtual machine.
Continuous MFA helps BPOs and their customers show their commitment to security while also:
- Meeting PCI DSS 4.0 compliance standards
- Eliminating costly hard tokens
- Saving 40 minutes per agent per month
- Protects your brand and reputation with a best-in-class identity security policy

.jpeg)
.jpeg)
