Twosense provides software-based continuous authentication in the workplace, for better security with better productivity. We provide Continuous Identity Assurance, with the goal of automating human effort and human error out of Identity Security completely.
We’ve been working with the US DoD for years, but today we’re excited to announce that we’ve been welcomed into the Okta Integration Network:
“Twosense provides cutting edge security for the future of work. As teams move remote, new solutions are needed that enable productivity while helping customers move towards Zero Trust security. Twosense and continuous authentication are such a solution. We're excited to have Twosense join the Okta Integration Network, and to be working with them on the future of continuous identity assurance.”
—Stephen Lee, VP of Tech Strategy and Partnerships at Okta
Here we’d like to share a bit about continuous authentication and why that’s so important right now, and how our product integrates continuous authentication into Okta Single Sign-On. Over the coming months, we’ll be working closely with Okta to bring Continuous Authentication and Continuous Identity Assurance to Enterprise. Here’s why this is such an important step in the corporate security landscape.
THE PROBLEM
Multi-factor authentication, or MFA, is secure, but only if we use it everywhere and often, so the user experience is the limiting factor (users really hate MFA). As the world moves remote, with 90% of work happening outside the perimeter, organizations are sprinting towards Zero Trust. Zero Trust is not a technology, but a concept: don’t trust any device or connection unless you see proof that you should. For Zero Trust identity security at the user level, that translates into many repetitive MFA challenges, causing what NIST calls “Security Fatigue” that kills productivity. Enterprises are now forced to decide between real Zero Trust identity security, and the employee user experience and productivity.
.png?width=850&name=Remote%20Work%2c%20Zero%20Trust%2c%20and%20Multi-Factor%20Authentication%20(4).png)
The Move to Zero Trust is Forcing Hard Decisions Between Security and Usability.
What’s the solution? According to NIST, the solution is continuous authentication based on user behavior.
THE SOLUTION
The Twosense product is a browser extension that integrates with Okta Single Sign-On. It observes user behavior and builds a behavioral profile of each user individually for continuous authentication. Continuous authentication responds to MFA challenges on the user’s behalf, so the user is only confronted with MFA as a last resort. Continuous authentication is powered by Behavioral Biometrics, which run invisibly in the background, creating a running trust score for dynamic access control across the session.
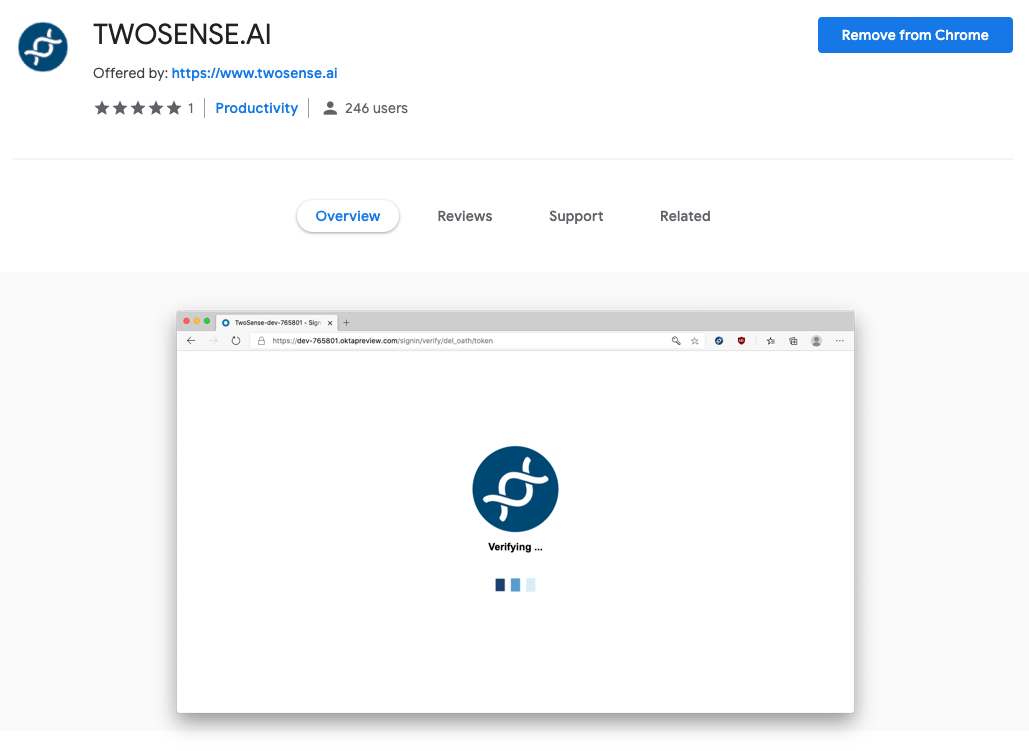
The Twosense Browser Extension is available from Extension Web Stores and deploys easily, available the same day.
Our products accomplish this by looking at every measurable aspect of human behavior to build a holistic profile of each user. We use motion sensors to observe a user’s gait, for example, quantifying aspects such as the length of their stride and impact of footfall, or even muscle tremors as they hold a device. In total, we observe hundreds of factors, which are modeled for each user individually with advanced deep learning. This product, specifically, lives in the browser, and so it focuses on the behavioral factors that can be utilized there. Typing behavior, for example, quantifies aspects such as speed, cadence and variability of typing, as well as errors specific to this user. Mouse behavior quantifies aspects acceleration and deceleration, over and undershooting of targets, click and double-click rates, press times, etc. Combined with application usage, temporal patterns, and IP location, we can get a full answer to a question like: “Is this the behavior of the authorized user for this application at this time and location?” It’s important to note that we do not store any PII. We don’t know who the user is, and we don't even need to know what the user is doing, just how they're doing it.
The Twosense browser extension continuously monitors user behavior and synchronizes with our cloud which continuously updates the trust score. When the user logs in, Okta requests verification from Twosense. If the user is verified Okta grants access. Otherwise, Okta falls back to the default MFA (e.g. Okta Verify, Duo, etc.) before granting access. Up to 95% of MFA challenges are eliminated by continuous authentication. You can take a look at a demo below and experience this for yourself.
WHO IT’S FOR
Our product is ideal for Okta SSO customers moving towards Zero Trust and looking for tools to achieve this, or customers who have already implemented a Zero Trust architecture and are looking for ways to improve the user experience and avoid security fatigue. Continuous authentication is a core tenet (#6) of any Zero Trust Architecture according to NIST’s Zero Trust guidelines SP800-207. Our product is integrated as a SAML 2.0 IdP factor, and deployment is simple. The admin needs to add our SAML 2.0 IdP, exchange certificates, and deploy a browser extension using group policies. The entire process usually takes less than 30 minutes and is available that same day.
WHERE WE’RE GOING
Today, we’re using Continuous Authentication to respond to MFA challenges on the user’s behalf. Over the next few months, we’ll be working with the team at Okta to integrate our real-time Continuous Identity Assurance across the session. In the future, new standards such OpenID Connect’s Continuous Access Evaluation Protocol (CAEP) will enable continuous authentication to escalate and deescalate security in real-time, as well as extend and terminate sessions based on trust scores. While Okta is a first mover, MSFT, CoinBase, Amazon, Duo and many more are all engaged in the drafting of CAEP, acknowledging the move towards a world of Continuous Identity Assurance.
We are extremely excited to be working with the Okta team on this initiative. Together, we will be making large strides over the next months towards eliminating human effort and human error out of Identity Security entirely. For now, you can find us in the Okta Integration Network (OIN) or on our website at www.twosense.ai/okta. Feel free to reach out and schedule a demo, or sign up for our upcoming webinar to become a part of the future of Enterprise employee identity.
.jpeg)
.jpeg)
.png)