Twosense Solves the Top Security and Compliance Challenges Facing Contact Centers
Our behavior-based authentication, driven by typing patterns and mouse movements, automates tackling phishing, fraud, and password sharing while ensuring clean desk compliance with PCI 4 standards—without relying on phones or hard tokens.



.png?width=500&height=249&name=Untitled%20(9).png)

.png?width=370&height=129&name=Generic%20Logos%20(2).png)
Discover Why Leading BPOs & Contact Centers Trust Twosense
Book Your Personalised Live Demo: Experience how Twosense can transform your security and compliance operations.
Solve Key Security & Compliance Challenges: See Twosense in action, tackling the most pressing issues in contact centers today.
Simplify Your Security Management: Learn how Twosense streamlines security processes, keeping your operations compliant with ease.
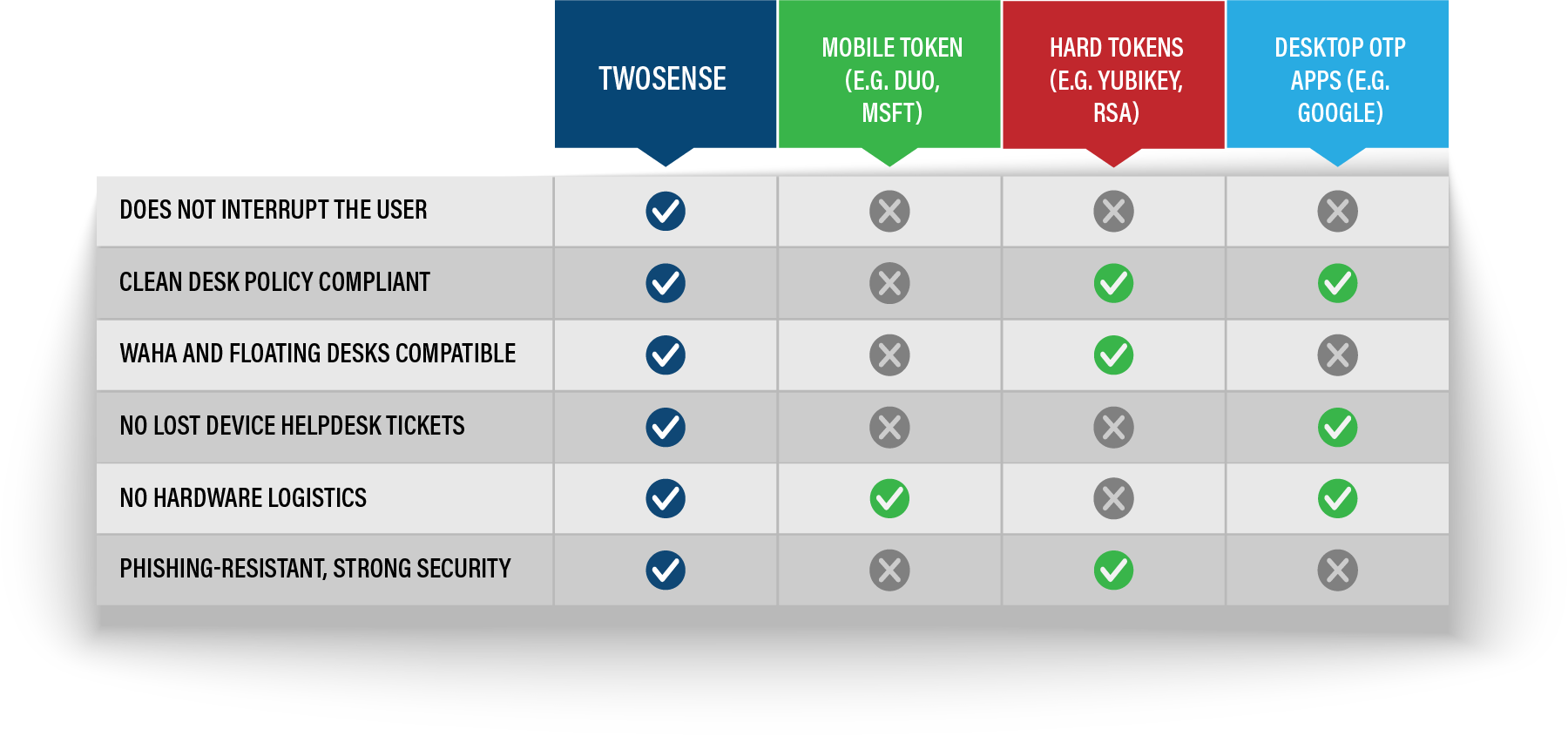
Phones & Hard Tokens Don't Work For BPOs Contact Centers
Multi-factor authentication (MFA) is essential for BPO contact centers, yet traditional methods fall short. Strict clean desk policies limit the use of mobile-based MFA, while hardware tokens present logistical and financial challenges, making them difficult to scale.
BPO Contact Center Security Made Easy
User authentication should be continuous, compliant, and phishing-resistant. Twosense is simple, clean-desk compliant authentication that works for you!
Twosense holds the key to addressing the challenges that we face in enterprise authentication. A solution that is simple, cost effective & compliant!
Our clients were amazed with Twosense. Even if our employee’s password were stolen, there is no way we would be at risk.
Twosense strengthens our security identity and ensures operational continuity and PCI compliance, providing a secure environment for our operations.
Twosense’s AI-powered solution is a game changer for our industry. It provides bulletproof security while enhancing both productivity and the user experience.
What Is Behavioral Authentication?
Behavioral authentication is a factor of multi-factor authentication (MFA) that verifies a user's identity based on unique aspects of their behavior, like how they type or move their mouse. It dynamically analyzes a user's natural patterns of interaction to build a profile that can recognize suspicious deviations.
Continuous MFA provides continuous, persistent authentication by constantly monitoring how someone interacts with their device. Even if credentials are compromised, a fraudster won't be able to mimic a user's distinct behavior.
Continuous authentication refers to the ongoing process of verifying the identity of a user throughout their entire session or interaction with a system rather than just at the initial login. This approach enhances security by constantly monitoring and validating the user's identity, reducing the risk of unauthorized access.
By leveraging user behavior and machine learning, Twosense builds a model of each user's behavior, which can then be used to create a baseline of trust and continuously validate the user's identity throughout the day based solely on their digital behavior.
Phishing-resistant Multi-Factor Authentication (MFA) refers to an authentication method designed to mitigate the risks associated with phishing attacks. Phishing is a type of cyber attack where attackers trick individuals into divulging sensitive information, such as usernames, passwords, or other credentials, by posing as a trustworthy entity.
Behavioral MFA is 100% software, meaning no keys or codes can be compromised during a phishing attempt.
Yes. According to PCI SSC, NIST, and the European Commission, behavioral biometrics do meet PCI 4 and PSD2 requirements for multi-factor authentication.
To learn more about Continuous MFA and PCI compliance, please read our Becoming PCI DSS 4.0 Compliant with Behavioral Biometrics, here.
Becoming PCI Compliant With Twosense Continuous MFA
Contact centers need an identity security solution that is more versatile than traditional MFA. PCI v4.0 requires MFA, but achieving PCI compliance can be almost impossible in secure contact centers. With most contact centers adhering to strict clean desk policies, multi-factor authentication that relies on mobile phones or text messages is impossible to deploy, and hard tokens are difficult and expensive to manage and scale.
Twosense is “something you are” that’s 100% software and can be easily deployed onto any Windows workstations or VDI infrastructure.

